- Home
- Discover
Dew Solutions specialises in a suite of Application Development that is mission critical for business and enterprise, for clients across the world.
We are expanding rapidly and are working on several cutting technologies across various domains. We have some of the best in the industry working with us and are looking for young and bright minds to join us.
- Discover
- What we do
- Who we serve
We are a team of specialists with experience in a gamut of technologies and domains.
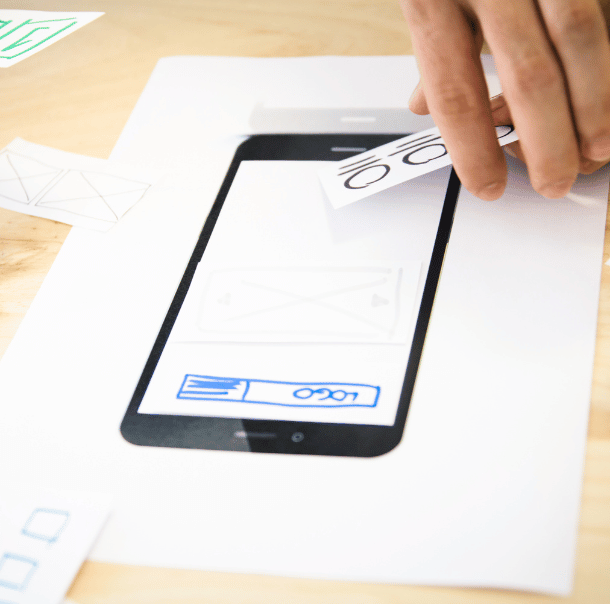
We possess a deep understanding of different languages and tools in the areas of design, development, and testing. Certified and experienced, our team combines technical know-how with industry best practices to create sustainable solutions.
We deliver bespoke industry specific solutions leveraging our extensive digital experience, design-led engineering approach and agile processes backed by our strong expertise in cutting edge technologies
- COE
To nurture the technical prowess of these solution providers and strengthen our offerings further – Dew Solutions has institutionalised various Centres of Excellence (CoEs).
These Centres of Excellence drive the experience and excellence which we want to deliver to our customers. Our subject matter experts in these CoEs collaborate with our customers to co-create and co-innovate thereby empowering them with ‘real’ solutions which their business needs.
- COE






